Producers are the preferred company targets for ransomware assaults and id and knowledge theft. With buyer orders and deliveries hanging within the stability, they will solely afford to have their product strains down for a short while. So attackers know that if they will disrupt manufacturing operations, they will pressure a excessive ransom payout.
Pella Company’s method to zero belief gives a realistic, useful roadmap for producers seeking to modernize their cybersecurity. Pella is a number one window and door producer for residential and industrial clients, and has been in enterprise since 1925.
>>Don’t miss our particular subject: The search for Nirvana: Making use of AI at scale.<<
VentureBeat not too long ago had the chance to interview John Baldwin, senior supervisor, cybersecurity and GRC at Pella Company. He described Pella’s progress towards a zero-trust mindset, beginning with bettering safety for five,200 endpoints and 800 servers corporate-wide, and fine-tuning its governance framework. Pella makes use of CrowdStrike Falcon Full managed detection and response (MDR) and Falcon Id Menace Safety for endpoint safety to scale back the chance of identity-based assaults. The methods are defending 10,000 workers, 18 manufacturing areas and quite a few showrooms.
Baldwin instructed VentureBeat that the corporate’s method to zero belief is “a mindset, and a bunch of overlapping controls. CrowdStrike shouldn’t be going to be the one participant in my zero-trust deployment, however they are going to be a key a part of that after all. Endpoint visibility and safety, you’ve obtained to start out there. After which constructing the governance framework to the following layer, baking that into id, ensuring that all your agile DevOps have gotten agile DevSecOps.”
Manufacturing lives and dies on availability
Producers are prime targets for attackers as a result of their companies are essentially the most time-sensitive — and since their IT infrastructures are the least safe. Baldwin instructed VentureBeat that “like most just-in-time producers, we’re fairly delicate to disruptions. In order that’s been an space of explicit focus for us. We need to make sure that as orders are flowing in, the product is flowing out as quickly as we will so we will fulfill buyer calls for. That’s been a problem. We’ve seen loads of different organizations in our business and all through the Midwest … simply attempting to get by way of the day being focused as a result of, as just-in-time producers or service suppliers, they’re very delicate to issues like a ransomware assault.”
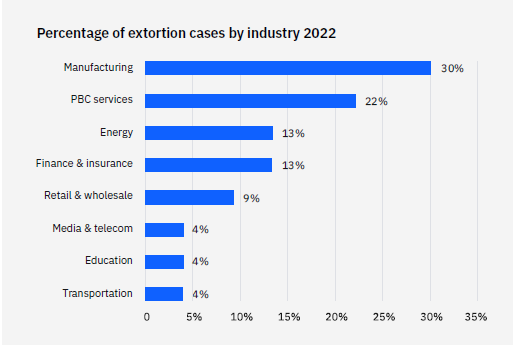
IBM’s X-Drive Menace Intelligence Index 2023 discovered that manufacturing continues to be the most-attacked business, and by a barely bigger margin than in 2021. The report discovered that in 2022, backdoors have been deployed in 28% of incidents, beating out ransomware, which appeared in 23% of incidents remediated by X-Drive. Knowledge extortion was the main affect on manufacturing organizations in 32% of instances. Knowledge theft was the second-most frequent at 19% of incidents, adopted by knowledge leaks at 16%.

Pella’s Baldwin instructed VentureBeat that the risk panorama for manufacturing has shifted from opportunistic ransomware assaults to assaults from organized criminals. “It isn’t a matter of if they arrive, however when, and what we will do about it,” he stated. “In any other case, we might undergo a methods outage for a number of days, which might disrupt manufacturing and be very expensive, to not point out the delays impacting our clients and enterprise companions.
Producers’ methods are down a mean of 5 days after a cyberattack. Half of those firms reported that they reply to outages inside three days; solely 15% stated they reply in a day or much less.
“Manufacturing lives and dies primarily based on availability,” Tom Sego, CEO of BlastWave, instructed VentureBeat in a latest interview. “IT revolves on a three- to five-year expertise refresh cycle. OT is extra like 30 years. Most HMI (human-machine interface) and different methods are operating variations of Home windows or SCADA methods which might be now not supported, can’t be patched, and are excellent beachheads for hackers to cripple a producing operation.”
Pella’s pragmatic view of zero belief
The teachings realized from planning and implementing a zero-trust framework anchored in strong governance kind the inspiration of Pella’s ongoing accomplishments. The corporate is displaying how zero belief can present the wanted guardrails for holding IT, cybersecurity and governance, threat, and compliance (GRC) in sync. Most significantly, Pella is defending each id and risk floor utilizing zero-trust-based automated workflows that unencumber their many groups’ invaluable time. “How I envision zero belief is, it really works, and no person has to spend so much of time validating it as a result of it’s automated,” Baldwin instructed VentureBeat.
“The primary attraction of a zero-trust method, from my perspective, is that if I can standardize, then I can automate. If I can automate, then I could make issues extra environment friendly, probably cheaper, and above all, a lot, a lot simpler to audit.
“Beforehand,” he went on, “we had loads of handbook processes, and the outcomes have been okay, however we spent loads of time validating. That’s not likely that invaluable within the grand scheme of issues. [Now] I can have my group and different technical assets centered on tasks, not simply on ensuring issues are working appropriately. I assume that most individuals are like me in that sense. That’s rather more rewarding.”
Doubling down on id and entry administration (IAM) first
Baldwin instructed VentureBeat that “id permeates a zero-trust infrastructure and zero-trust operations as a result of I have to know who’s doing what. ‘Is that conduct regular?’ So, visibility with id is vital.”
The subsequent factor that should get achieved, he stated, is getting privileged account entry credentials and accounts safe. “Privileged account administration is part of that, however id might be even increased within the hierarchy, so to talk. Locking down id and having that visibility, notably with CrowdStrike Falcon Id Safety, that’s been certainly one of our largest wins. If you happen to don’t have a great understanding of who’s in your atmosphere, then [problems become] a lot tougher to diagnose.
“Merging these two collectively [securing accounts and gaining visibility] is a recreation changer,” he concluded.
Going all-in, early, on least-privilege entry
“Pella has lengthy enforced a, we’ll name it, least privileges method. That allowed us to isolate areas that had accrued some extra privileges and have been inflicting extra points. We began dialing again these privileges, and you recognize what? The issues additionally went away. So, that’s been very useful,” Baldwin stated. “One other factor that I’ve been more than happy with is, it offers us a greater concept of the place gadgets drop off our area.”
Establishing endpoint visibility and management early in any zero-trust roadmap is desk stakes for constructing a strong basis that may assist superior strategies, together with community and id microsegmentation. Pella realized how vital it was to get this proper and determined to delegate it to a managed 24/7 safety operations heart run by CrowkdStrke and its Falcon Full Service.
“We’ve been extraordinarily glad with that. Then I used to be one of many early adopters of the Id Safety Service. It was nonetheless referred to as Preempt once we bought it from CrowdStrike. That has been implausible for having that visibility and understanding of what’s regular conduct primarily based on id. If a person is logging into these identical three gadgets on a routine foundation, that’s nice, but when the person immediately begins attempting to log into an lively listing area controller, I’d prefer to learn about that and possibly cease it.”
Know what zero-trust success seems to be like
Pella’s method to zero belief facilities on sensible insights it might probably use to anticipate and shut down any sort of assault earlier than it begins. Of the various producers VentureBeat has spoken with about zero belief, almost all say that they need assistance maintaining with their proliferating variety of endpoints and identities as their manufacturing operations shift to assist extra reshoring and nearshoring nearshoring. They’ve additionally instructed VentureBeat that perimeter-based cybersecurity methods have confirmed too rigid to maintain up.
Pella is overcoming these challenges by taking an identity-first method to zero belief. The corporate has decreased stale and over-privileged accounts by 75%, considerably decreasing the company assault floor. It has additionally diminished its incident decision from days to half-hour and alleviated the necessity to rent six full-time workers to run a 24/7 safety operations heart (SOC) now that CrowdStrike is managing that for them.
Pella’s recommendation: Consider zero belief as TSA PreCheck for identity-based entry
Baldwin says his favourite method to explaining zero belief is to make use of an allegory. His favourite is as follows: “So when folks ask me, what do you imply by zero belief? I say, ‘You’ve skilled zero belief each time you enter a industrial airport.’ It’s a must to have id info offered upfront. They’ve to grasp why you’re there, what flight you’re taking … Don’t carry this stuff to the airport, three-ounce bottles, no matter, all of the TSA guidelines. You then undergo a typical safety screening. You then … behave expectedly. And in case you misbehave, they’ll intervene.”
He continued, “So when folks go, ‘Oh, that’s what zero belief is,’ I’m considering, yeah, I’m attempting to construct that airport expertise, maybe with higher ambiance and a greater person expertise. However in the long run, in case you can observe all of these guidelines, you shouldn’t have any drawback getting from improvement to check to QA to deployed to manufacturing and have folks use it. If you’re a, we’ll say, safety practitioner, good in your discipline, possibly you possibly can join that TSA PreCheck, and you may have a pace move.”
Pella’s imaginative and prescient of zero belief is offering PreCheck for each system person globally, not slowing down manufacturing however offering identity-based safety on the scale and pace wanted to maintain manufacturing and fulfilling buyer orders.