Head over to our on-demand library to view classes from VB Remodel 2023. Register Right here
Capitalizing on malware-free tradecraft to launch undetectable breaches, attackers depend on respectable system instruments and living-off-the-land (LOTL) strategies to breach endpoints undetected. Malware-free assaults commerce on the belief of respectable instruments, not often producing a novel signature and counting on fileless execution.
Throughout all malicious exercise tracked by CrowdStrike and reported of their 2023 Menace Searching Report, 71% of detections listed by the CrowdStrike Menace Graph had been malware-free. A complete of 14% of all intrusions relied on distant monitoring and administration (RMM) instruments based mostly on exercise tracked by Falcon OverWatch. Attackers elevated their use of RMM instruments for malware-free assaults by an astounding 312% year-over-year.
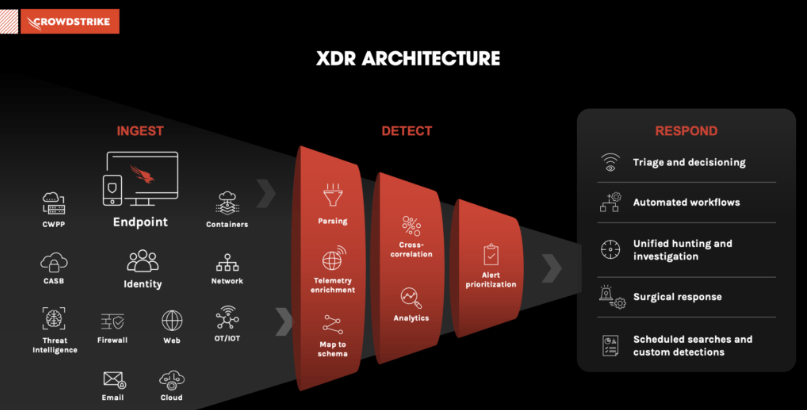
With FraudGPT signaling the beginning of a brand new period of weaponized AI and enterprises prone to dropping the AI conflict, the combination of AI, machine studying (ML) and generative AI into Prolonged Detection and Response (XDR) must be fast-tracked to thwart malware-free and new AI-driven assaults. XDR delivers the consolidation CISOs have been asking for.
XDR improves the signal-to-noise ratio
By counting on APIs and platforms designed to combine at scale, XDR platforms profit from each out there knowledge telemetry supply to detect and reply to potential intrusions and breach makes an attempt in actual time. These platforms are proving efficient in lowering noise throughout networks and discovering the indicators signifying a possible intrusion or assault.
Occasion
VB Remodel 2023 On-Demand
Did you miss a session from VB Remodel 2023? Register to entry the on-demand library for all of our featured classes.
Register Now
XDR is an efficient consolidation technique for CISOs: 96% plan to consolidate their safety platforms, with 63% saying(XDR is their high resolution selection, in accordance with Cynet’s 2022 survey of CISOs.
Almost all CISOs surveyed stated they’ve consolidation on their roadmaps, up from 61% in 2021. Gartner predicts that by year-end 2027, XDR will likely be utilized by as much as 40% of enterprises to cut back the variety of safety distributors they’ve in place, up from lower than 5% immediately.
An attribute all XDR leaders have is deep expertise density in AI and ML throughout their groups. Main XDR platform suppliers embody Broadcom, Cisco, CrowdStrike, Fortinet, Microsoft, Palo Alto Networks, SentinelOne, Sophos, TEHTRIS, Development Micro and VMWare.

Getting XDR proper: Begin with endpoints
Endpoints are the stealth on-ramp of selection for large-scale breach makes an attempt: Attackers use stolen identities greater than 62% of the time to realize entry and are always fine-tuning the tradecraft to seek out gaps in identification and endpoint safety, the weakest space of an endpoint.
Insurance coverage, monetary providers and banking CISOs inform VentureBeat that endpoints are essentially the most difficult menace floor to guard. It’s frequent for IT and safety groups to not know what number of endpoints they’ve, the place every endpoint is and its software program invoice of supplies (SBOM). Cleansing up endpoint agent sprawl and automating patch administration are the objectives many CISOs start with.
CISOs say it’s frequent to find that endpoints are overloaded with brokers to the purpose of being inoperable from a safety standpoint. Software program conflicts go away endpoints extra weak to assault, make them tougher to handle remotely and may scale back efficiency.
The Absolute Software program 2023 Resilience Index used nameless telemetry knowledge of its 500 million endpoint units to see what number of endpoints, on common, their prospects have. They discovered that the standard enterprise gadget has 11 safety brokers put in, with 2.5 for endpoint administration, 2.1 for antivirus/antimalware and 1.6 on common for encryption. Absolute gadget telemetry knowledge discovered 67 functions put in on the common enterprise gadget, with 10% of these units having greater than 100 put in.
Automating endpoint patch administration
The CIO of a number one producer informed VentureBeat that whereas patching is all the time a excessive precedence, she doesn’t have sufficient employees to maintain all patches present. CISO colleagues agree that patch administration solely will get consideration when it’s an emergency — after an intrusion or breach. That conclusion is per Ivanti’s State of Safety Preparedness 2023 Report. Ivanti discovered that 61% of the time, an exterior occasion, intrusion try or breach reinitiates patch administration efforts.
“Patching isn’t practically so simple as it sounds,” stated Srinivas Mukkamala, chief product officer at Ivanti. “Even well-staffed, well-funded IT and safety groups expertise prioritization challenges amidst different urgent calls for. To scale back threat with out rising workload, organizations should implement a risk-based patch administration resolution and leverage automation to determine, prioritize, and even handle vulnerabilities with out extra guide intervention.”
Mukkamala informed VentureBeat that he envisions patch administration turning into extra automated, with AI copilots offering higher contextual intelligence and prediction accuracy.
“With greater than 160,000 vulnerabilities presently recognized, it’s no marvel that IT and safety professionals overwhelmingly discover patching overly complicated and time-consuming,” he stated. “That is why organizations should make the most of AI options … to help groups in prioritizing, validating and making use of patches. The way forward for safety is offloading mundane and repetitive duties fitted to a machine to AI copilots in order that IT and safety groups can give attention to strategic initiatives for the enterprise.”

AI Strengthening XDR resilience with self-healing endpoints
Getting cyber-resilience proper in a zero-trust world begins with the endpoint. Boards of administrators and the CISOs briefing them say cyber-resilience is now thought-about vital for threat administration. Absolute Software program’s 2023 Resilience Index displays the problem of excelling on the comply-to-connect pattern. Balancing cybersecurity and cyber-resilience is the purpose.
CISOs inform VentureBeat that self-healing endpoints are the cornerstones of a strong cyber-resilience technique. Endpoints that heal themselves present a dependable, real-time stream of telemetry knowledge to coach AI and ML fashions and strengthen XDR platforms. They’re additionally tougher to evade and breach in comparison with their previous-generation constraint and rules-based counterparts. AI and ML-based endpoints detect and reply to potential assaults in milliseconds, which is desk stakes for immediately’s enterprises, given the fast rise in machine-to-machine assaults.
Main self-healing endpoint suppliers embody Absolute Software program, Akamai, BlackBerry, CrowdStrike, Cisco, Malwarebytes, McAfee and Microsoft 365. VentureBeat has interviewed prospects of every vendor and located that Absolute’s strategy to being embedded within the firmware of over 500 million endpoint units is essentially the most dependable in offering SOC groups with the real-time telemetry knowledge they and their XDR platforms want.
Absolute’s strategy is exclusive in its reliance on firmware-embedded persistence as the idea of self-healing, offering an undeletable digital tether to each PC-based endpoint. Absolute Software program’s Resilience, the business’s first self-healing zero belief platform, is noteworthy for its asset administration, gadget and software management, endpoint intelligence, incident reporting and compliance.
XDR: The primary line of protection towards weaponized AI
The period of weaponized AI is right here, and XDR platforms have to step up and tackle the problem of getting all the worth they will out of AI and ML applied sciences if the cybersecurity business and the various organizations they serve are going to remain secure. Nobody can afford to lose the AI conflict towards attackers who see the gaps in identities and endpoints as a possibility to take management of networks and infrastructure.
What’s most troubling is that legacy perimeter-based techniques assumed limitless belief in each identification, endpoint and connection, offering attackers with unchecked entry to any system as soon as they compromised an endpoint. Getting XDR proper wants to begin with endpoints. Cleansing up agent sprawl helps enhance endpoint visibility and efficiency, and automating patch administration with AI and ML strategies that study as an alternative of ready for the subsequent breach saves IT groups from fireplace drills and wasted time.
Self-healing endpoints are the cornerstone of cyber-resilience. Getting these areas sturdy is a prerequisite for taking advantage of an XDR structure that may ship on its potential to guard a company’s core enterprise capabilities and prospects.