Be a part of high executives in San Francisco on July 11-12, to listen to how leaders are integrating and optimizing AI investments for fulfillment. Be taught Extra
Endpoints should turn out to be extra clever, resilient and self-healing to help the various new identities they should defend. Even essentially the most hardened endpoints are in danger as a result of they’ll’t defend in opposition to identity-based breaches. Placing any belief in identities is a breach ready to occur.
How endpoint safety platform (EPP), endpoint detection and response (EDR) and prolonged detection and response (XDR) suppliers reply to the problem will outline the way forward for endpoint safety. Primarily based on the various briefings VentureBeat has had with main suppliers, a core set of design aims and product route emerges. Collectively, they outline endpoint safety’s future in a zero-trust world.
Srinivas Mukkamala, chief product officer at Ivanti, suggested organizations to contemplate each working system and have the flexibility to handle each person profile and shopper system from one single pane of glass. Staff need to entry work knowledge and programs from the system of their selection, so safety in offering entry to gadgets ought to “by no means be an afterthought.”
“Enterprise leaders will proceed to see prices of managing these gadgets rise in the event that they don’t think about the number of gadgets workers use,” stated Mukkamala. “Organizations should proceed transferring towards a zero-trust mannequin of endpoint administration to see round corners and bolster their safety posture.”
Occasion
Remodel 2023
Be a part of us in San Francisco on July 11-12, the place high executives will share how they’ve built-in and optimized AI investments for fulfillment and prevented frequent pitfalls.
Register Now
Producers, specifically, name ransomware assaults that capitalize on unprotected endpoints a digital pandemic. And, after an assault, the forensics present how attackers are fine-tuning their tradecraft to capitalize on weak to non-existent endpoint id safety.
CrowdStrike’s 2023 World Risk Report found that 71% of all assaults are malware free, up from 62% in 2021. CrowdStrike attributes this to attackers’ prolific use of legitimate credentials to achieve entry and carry out long-term reconnaissance on focused organizations. One other contributing issue is how rapidly new vulnerabilities are publicized and the way rapidly attackers transfer to operationalize exploits.
CrowdStrike president Michael Sentonas advised VentureBeat that the intersection of endpoint and id is without doubt one of the largest challenges right now.
Attackers doubling down on enhancing their tradecraft lowered the common breakout time for intrusion exercise from 98 minutes in 2021 to 84 minutes in 2022. CrowdStrike notes that it may take as much as 250 days for organizations to detect that an id breach has occurred when attackers have legitimate credentials to work with.
Main EPP, EDR and XDR suppliers hear from prospects that identity-based endpoint breaches are rising. It’s not shocking that 55% of cybersecurity and threat administration professionals estimate that greater than 75% of endpoint assaults can’t be stopped with their present programs.
Generative AI must ship zero-trust positive factors
Generative AI might help seize each intrusion, breach and anomalous exercise together with their causal components to higher predict and cease them. With these instruments, safety, IT and operations groups will be capable of study from every breach try and collaborate on them. Generative AI will create a brand new sort of “muscle reminiscence” or reflexive response.
Notable suppliers with robust AI and machine studying (ML) leads embrace CrowdStrike, Cisco, Ivanti, Microsoft, Palo Alto Networks and Zcaler. Microsoft spent $1 billion in cybersecurity R&D final yr and dedicated to spending one other $20 billion over the subsequent 5 years.
Suppliers search stepwise positive factors to offer extra contextual intelligence, resilience and self-healing. It’s simple to see why endpoint suppliers together with BitDefender, Cisco, Ivanti, McAfee, Palo Alto Networks, Sophos and others are doubling down on AI and ML to deliver a brand new depth to how they innovate.
Beneath are key takeaways from product briefings with main suppliers.
Quick-tracking ML apps to determine most crucial CVEs impacting endpoints
Energetic Listing (AD), first launched with Home windows Server in 2019, remains to be used throughout tens of millions of organizations. Attackers usually goal AD to achieve management over identities and transfer laterally throughout networks. Attackers exploit AD’s long-standing CVEs as a result of organizations prioritize essentially the most pressing patches and CVE defenses first.
Undoubtedly, AD is underneath assault; CrowdStrike discovered that 25% of assaults come from unmanaged hosts like contractor laptops, rogue programs, legacy purposes and protocols and elements of the provision chain the place organizations lack visibility and management.
Consolidating tech stacks gives higher visibility
CISOs say that budgets are underneath larger scrutiny, so consolidating the variety of purposes, instruments and platforms is a excessive precedence. The bulk (96%) of CISOs plan to consolidate their safety platforms, with 63% preferring (XDR). Consolidating tech stacks will assist CISOs keep away from lacking threats (57%), discover certified safety specialists (56%) and correlate and visualize findings throughout their menace panorama (46%).
All main suppliers at the moment are pursuing consolidation as a development technique, with CrowdStrike, Microsoft and Palo Alto Networks essentially the most usually CISOs point out to VentureBeat.
CISOS says that Microsoft is essentially the most difficult to get proper of the three. Microsoft sells Intune as a platform that helps lower prices as a result of it’s already included in current enterprise licenses. However, CISOs say they want extra servers and licenses to deploy Intune, making it costlier than they anticipated. CISOs additionally say managing all working programs is difficult, they usually want extra options to cowl their total IT infrastructure.
CrowdStrike, in the meantime, makes use of XDR as a consolidation platform; Ivanti fast-tracks AI and ML-based enhancements to UEM; and Palo Alto Networks’ platform-driven technique goals to assist prospects consolidate tech stacks. Throughout his keynote at Fal.Con 2022, CrowdStrike cofounder and CEO George stated that endpoints and workloads present 80% of essentially the most useful safety knowledge.
“Sure, [attacks] occur throughout the community and different infrastructure,” he stated. “However the actuality is individuals are exploiting endpoints and workload.”
Jason Waits, CISO at Inductive Automation, defined that his firm consolidated vulnerability scanning and endpoint firewall administration into the CrowdStrike agent, eradicating two separate safety instruments within the course of.
“Decreasing the variety of brokers we have to set up and preserve considerably reduces IT administration overhead whereas enhancing safety,” he stated.
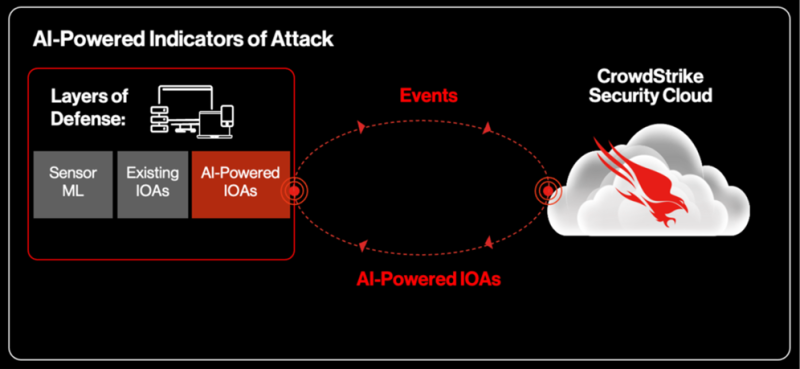
Contextual intelligence AI-based indicators of assault (IOA) core to fixing endpoint-identity hole
By definition, indicators of assault (IOA) gauge a menace actor’s intent and attempt to determine their objectives, whatever the malware or exploit used. Complementing IOAs are indicators of compromise (IOC) that present forensics to show a community breach. IOAs should be automated to offer correct, real-time knowledge to know attackers’ intent and cease intrusion makes an attempt.
VentureBeat spoke with a number of suppliers who’ve AI-based IOA underneath growth and discovered that CrowdStrike is the primary and solely supplier of AI-based IOAs. The corporate says AI-powered IOAs work asynchronously with sensor-based ML and different sensor protection layers. The corporate’s AI-based IOAs use cloud-native ML and human experience on a platform it invented over a decade in the past. AI-generated IOAs (behavioral occasion knowledge) and native occasions and file knowledge are used to find out maliciousness.

Standalone instruments don’t shut gaps between endpoints and identities; platforms do
Normalizing experiences throughout numerous standalone instruments is tough, time-consuming and costly. SOC groups use guide correlation strategies to trace threats throughout endpoints and identities. Instruments don’t have a typical set of alerts, knowledge buildings, reporting codecs and variables, so getting all exercise on a single pane of glass isn’t working.
Ivanti Neurons for UEM depends on AI-enabled bots to hunt out machine identities and endpoints and mechanically replace them. Their strategy to self-healing endpoints combines AI, ML and bot applied sciences to ship unified endpoint and patch administration at scale throughout a world enterprise buyer base.

Self-healing endpoints assist shut the hole whereas delivering resilience
Essentially the most superior UEM platforms can combine with and allow enterprise-wide micro-segmentation, IAM and PAM. When AI and ML are embedded in platforms and endpoint system firmware, enterprise adoption accelerates. Self-diagnostics and adaptive intelligence make a self-healing endpoint. Self-healing endpoints can flip themselves off, recheck OS and utility versioning and reset to an optimized, safe configuration. These actions are autonomous, with no human interplay wanted.
CISOs inform VentureBeat that cyber-resiliency is as crucial to them as consolidating their tech stacks. The telemetry and transaction knowledge that endpoints generate are among the many most respected sources of innovation the zero-trust vendor group has right now. Count on additional use of AI and ML to enhance endpoint detection, response and self-healing capabilities.
Conclusion
Endpoint safety in a zero-trust world is determined by EPP, EDR and XDR suppliers’ means to bridge the endpoint safety and id safety hole on a single platform utilizing frequent telemetry knowledge in real-time. Primarily based on interviews VentureBeat carried out with main suppliers and CISOs, it’s evident that this may be achieved utilizing generative AI to ship zero-trust positive factors and consolidate tech stacks for higher visibility. Suppliers should innovate and combine AI and ML applied sciences to enhance endpoint detection, response and self-healing within the face of a fast-changing and unforgiving menace panorama.